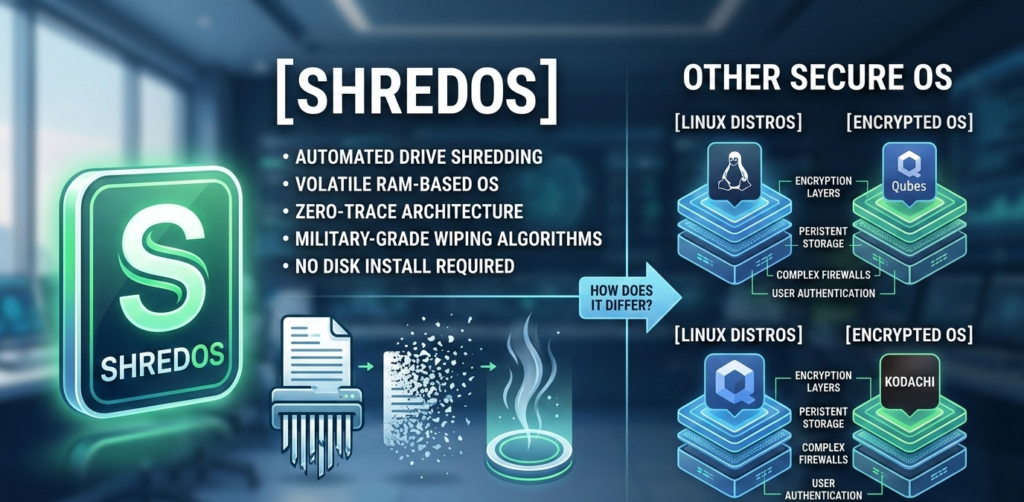
How does ShredOS differ from other secure operating systems? ShredOS is designed to provide unmatched security and privacy features that set it apart from traditional secure operating systems. Unlike standard systems, ShredOS focuses on data shredding, anonymous browsing, and robust encryption to ensure user information remains completely protected. Its lightweight design and streamlined interface make it efficient while maintaining high-level security, making ShredOS ideal for privacy-conscious individuals and organizations.
In comparison to other secure operating systems, ShredOS integrates advanced security protocols and real-time threat detection. With ShredOS, users benefit from unique features like secure file deletion, sandboxed applications, and minimized digital footprints, making it a standout choice in the realm of secure operating systems.
Core Security Architecture
Core Security Architecture refers to the foundational framework that ensures an organization’s digital systems, data, and network are protected against unauthorized access, cyber threats, and data breaches. It defines how security principles are implemented across hardware, software, and network resources to maintain integrity, confidentiality, and availability. Implementing a strong security architecture is critical for organizations to safeguard sensitive information and comply with industry regulations.
Security Framework and Principles
The first pillar of core security architecture is the security framework and principles. This defines the overall guidelines for securing organizational assets and digital infrastructure. It includes key principles like confidentiality, integrity, and availability—commonly known as the CIA triad. Confidentiality ensures sensitive data is accessible only to authorized personnel. Integrity guarantees that data remains accurate and unaltered. Availability ensures that systems and information are accessible when needed. Security frameworks such as ISO/IEC 27001, NIST Cybersecurity Framework, and CIS Controls provide organizations with structured methodologies to implement these principles effectively.
Network Security Architecture
Network security architecture forms the backbone of core security by protecting the organization’s internal and external network traffic. It focuses on designing secure network topologies, implementing firewalls, intrusion detection/prevention systems (IDS/IPS), and secure gateways. Proper segmentation of networks, VPNs for remote access, and secure protocols such as TLS/SSL are critical components. Network security ensures that malicious actors cannot exploit vulnerabilities, intercept data, or launch attacks like DDoS or man-in-the-middle. By enforcing strict access control, monitoring, and real-time threat detection, network security strengthens the overall security posture of an organization.
Identity and Access Management (IAM)
Identity and Access Management (IAM) is a crucial element of core security architecture that manages user identities and controls access to sensitive resources. IAM systems enforce strong authentication mechanisms, including multi-factor authentication (MFA), single sign-on (SSO), and role-based access control (RBAC). These measures prevent unauthorized access, insider threats, and credential misuse. By continuously monitoring user activity and adjusting permissions based on least privilege principles, IAM ensures that each user has access only to what is necessary for their role. Effective IAM implementation is vital for regulatory compliance and reduces the risk of data breaches significantly.
Data Security and Encryption
Protecting organizational data is a central focus of core security architecture. Data security and encryption involve safeguarding both data at rest and data in transit. Encryption algorithms such as AES-256 or RSA secure sensitive information, making it unreadable to unauthorized users. Additionally, secure data storage practices, backup strategies, and regular data audits strengthen protection. Organizations also implement data loss prevention (DLP) systems, which monitor and prevent sensitive data from leaving the network. Proper data classification, secure key management, and regulatory compliance, like GDPR or HIPAA, are also critical components of this subdomain.
Security Monitoring and Incident Response
Finally, security monitoring and incident response are essential for maintaining a proactive defense strategy. Continuous monitoring through security information and event management (SIEM) systems, intrusion detection, and threat intelligence allows organizations to detect anomalies in real-time. Incident response plans define the procedures to follow in case of security breaches, including containment, mitigation, communication, and post-incident analysis. Regular security audits, penetration testing, and vulnerability assessments ensure weaknesses are identified and mitigated promptly. This proactive approach minimizes downtime, protects critical assets, and strengthens the overall resilience of an organization’s digital environment.
Data Privacy and Encryption
In today’s digital age, protecting sensitive information is more important than ever. Data privacy and encryption are critical components that safeguard personal, organizational, and financial data from unauthorized access, breaches, or misuse. Organizations and individuals must understand these concepts to ensure the security and integrity of their digital assets.
Data Privacy
Data privacy refers to the proper handling, processing, and storage of personal and sensitive information. It ensures that data collected from users, customers, or employees is used responsibly and only for its intended purpose. Compliance with global regulations, such as GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act), is a key aspect of data privacy. By prioritizing data privacy, organizations can build trust with customers, prevent identity theft, and avoid legal penalties.
Importance of Encryption in Data Security
Encryption is the process of converting data into a coded format that is unreadable to unauthorized users. It is a vital tool for protecting data both at rest (stored data) and in transit (data being transmitted over networks). Encryption ensures that even if data is intercepted, it cannot be accessed without the correct decryption key. Modern encryption methods, such as AES (Advanced Encryption Standard) and RSA (Rivest-Shamir-Adleman), provide robust protection against cyberattacks and data breaches.
Types of Data Encryption
There are several types of encryption that organizations and individuals can implement:
- Symmetric Encryption: Uses a single key for both encryption and decryption. It is fast and suitable for large datasets.
- Asymmetric Encryption: Uses a public key for encryption and a private key for decryption, ensuring secure communication channels.
- End-to-End Encryption: Ensures that data is encrypted at the sender’s end and decrypted only by the intended recipient, commonly used in messaging apps.
- File-Level Encryption: Encrypts individual files to protect sensitive documents.
Disk-Level Encryption: Encrypts an entire hard drive or storage device, securing all data stored within.
Benefits of Implementing Data Privacy and Encryption
Adopting strong data privacy and encryption measures offers several advantages:
- Enhanced Security: Protects sensitive information from hackers and cyber threats.
- Regulatory Compliance: Helps meet legal requirements and avoid fines.
- Customer Trust: Builds confidence among clients that their data is handled securely.
- Data Integrity: Prevents unauthorized modification or tampering of data.
Risk Mitigation: Reduces the potential financial and reputational damage from data breaches.
Best Practices for Data Privacy and Encryption
To maximize the effectiveness of data protection, organizations should follow best practices:
- Conduct regular audits and risk assessments to identify vulnerabilities.
- Implement multi-factor authentication (MFA) for secure access.
- Use strong, regularly updated encryption protocols for all data.
- Train employees on data privacy policies and safe handling practices.
Maintain secure backup solutions to prevent data loss during attacks or system failures.
Memory and Storage Protection
Memory and storage protection are critical aspects of modern computing systems that ensure data integrity, security, and efficient system performance. They prevent unauthorized access, accidental data corruption, and malicious attacks. Effective memory and storage protection mechanisms are vital for both personal devices and enterprise systems, providing a secure computing environment. Below is a detailed breakdown of key aspects.
Importance of Memory Protection
Memory protection is essential to safeguard the system’s RAM (Random Access Memory) from unauthorized access or malicious activities. Without proper memory protection, a single faulty or malicious program could overwrite the memory used by other programs, causing system crashes, data corruption, or security breaches. Techniques like memory segmentation, paging, and access control help isolate program memory areas, ensuring stability and reliability of applications. For businesses and developers, robust memory protection is critical to prevent data loss and maintain operational continuity.
Techniques for Memory Protection
Several techniques are implemented to ensure memory protection. Segmentation divides memory into different segments, each with specific access rights, preventing programs from interfering with one another. Paging allows memory to be divided into fixed-size blocks, providing controlled access to each page. Modern systems also use access control mechanisms like read, write, and execute permissions to define what operations can be performed on specific memory regions. Additionally, hardware features like Memory Management Units (MMU) enforce these protections at the processor level, making unauthorized access extremely difficult.
Storage Protection Overview
Storage protection focuses on safeguarding long-term data stored on hard drives, SSDs, or cloud storage from corruption, theft, or accidental deletion. Storage protection mechanisms include encryption, access controls, and redundancy. Encryption ensures that even if data is stolen, it cannot be read without the correct decryption key. Access control lists (ACLs) and permissions manage which users or processes can read, modify, or delete files. Storage protection is vital for sensitive data such as financial records, personal information, or proprietary business data, ensuring compliance with privacy regulations and corporate policies.
Methods to Enhance Storage Security
To enhance storage security, organizations implement multiple layers of protection. Encryption techniques like AES (Advanced Encryption Standard) protect data at rest, while backup and replication provide data recovery options in case of failure or attacks. Access control policies prevent unauthorized modifications, and modern storage systems incorporate auditing and logging features to monitor access patterns and detect anomalies. Additionally, cloud providers often offer advanced storage protection tools, including data versioning and automated threat detection, ensuring maximum reliability and resilience.
Benefits of Memory and Storage Protection
Implementing robust memory and storage protection offers numerous advantages. It ensures system stability by preventing crashes caused by unauthorized memory access. It enhances data security, protecting sensitive information from breaches or cyberattacks. Additionally, it supports compliance with industry regulations and standards, safeguarding both personal and organizational data. Proper protection also improves system performance, as controlled memory access reduces errors and resource conflicts. Ultimately, memory and storage protection are fundamental for maintaining trust, reliability, and efficiency in modern computing environments.
Secure Boot and System Integrity
Maintaining the security and integrity of a computing system is crucial in today’s digital landscape. Secure Boot and system integrity mechanisms are foundational technologies that protect devices from unauthorized software and malware. They ensure that only trusted software can run on a device, preventing attacks that compromise the operating system, firmware, or hardware.
Secure Boot
Secure Boot is a security standard developed to ensure that a device boots using only software that is trusted by the Original Equipment Manufacturer (OEM). During system startup, Secure Boot checks the digital signatures of firmware and bootloader components. If the signatures are valid and trusted, the system continues booting; otherwise, the device halts the process to prevent the execution of malicious code. This process protects against rootkits and boot-level malware, which are particularly dangerous because they load before the operating system and security software can intervene.
Secure Boot is widely implemented in modern PCs, laptops, and even embedded systems. It provides a chain of trust, starting from firmware verification to operating system kernel validation. By enforcing strict authentication of boot components, Secure Boot ensures that the system starts in a known, secure state, creating a foundation for overall system integrity.
The Importance of System Integrity
System integrity refers to the state of a computing system in which its hardware, firmware, and software remain unaltered and function as intended. Maintaining system integrity is vital to protect sensitive data, prevent unauthorized access, and maintain compliance with security regulations. If system integrity is compromised, attackers can manipulate the operating system, inject malware, or access private information without detection.
Modern security frameworks rely on integrity measurements, such as cryptographic checksums and digital signatures, to continuously verify that system components are authentic and unmodified. A strong integrity verification process can detect tampering early, mitigate potential threats, and reinforce overall cybersecurity for both personal and enterprise systems.
How Secure Boot Enhances System Integrity
Secure Boot directly supports system integrity by enforcing a verification mechanism at the earliest stage of the boot process. By validating each component before execution, Secure Boot ensures that only approved and verified firmware, bootloaders, and kernel modules are loaded. This preemptive protection prevents attackers from embedding malware in low-level system software, which is often difficult to detect and remove once active.
Additionally, Secure Boot integrates with trusted platform technologies, such as TPM (Trusted Platform Module), to store cryptographic keys and certificates securely. This combination allows the system to maintain a verifiable chain of trust, making it exceedingly difficult for malicious software to compromise the integrity of the device without detection.
Threats Mitigated by Secure Boot
Secure Boot and integrity mechanisms address several critical security threats:
- Rootkits and Bootkits: Malware that infects the boot process and hides from antivirus software.
- Unauthorized Firmware Modification: Attackers attempting to inject malicious firmware into devices.
- Kernel-Level Attacks: Compromises at the core operating system level that bypass traditional security controls.
- Tampering with System Files: Ensuring OS files remain unaltered to prevent malicious manipulation.
- Supply Chain Attacks: Protecting devices against compromised software components from third-party vendors.
By blocking untrusted or unsigned code from executing, Secure Boot effectively neutralizes these threats, ensuring the device maintains operational and security integrity.
Best Practices for Maintaining System Integrity
To fully leverage Secure Boot and system integrity, organizations and individuals should follow these best practices:
- Enable Secure Boot in BIOS/UEFI on all compatible devices.
- Keep firmware and operating systems updated to benefit from the latest security patches.
- Use trusted certificates and digital signatures for all software and firmware components.
- Regularly monitor system integrity logs and alerts to detect unusual changes.
- Integrate with hardware security modules, such as TPM, for enhanced cryptographic protection.
Following these practices not only maximizes the protective benefits of Secure Boot but also ensures that overall system integrity is continuously maintained. Organizations implementing these measures can prevent advanced threats, comply with cybersecurity regulations, and protect critical data against malicious attacks.
Conclusion
ShredOS stands out from other secure operating systems through its robust privacy protocols, advanced encryption, and user-centric security design. Unlike conventional systems, it emphasizes complete data isolation, secure file shredding, and minimal attack surfaces, ensuring maximum protection against cyber threats. Its combination of seamless usability and stringent security measures makes ShredOS an ideal choice for users seeking both efficiency and uncompromising digital privacy in today’s threat-prone environment.